NK hackers attacked S Korean atomic energy think tank
By Kim So-hyunPublished : June 18, 2021 - 14:53
An opposition lawmaker claimed on Friday that a hacking unit of the North Korean intelligence agency attacked the internal network of a South Korean state-funded atomic energy think tank which holds critical information on nuclear power plants and nuclear materials.
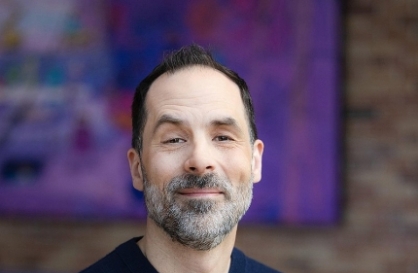
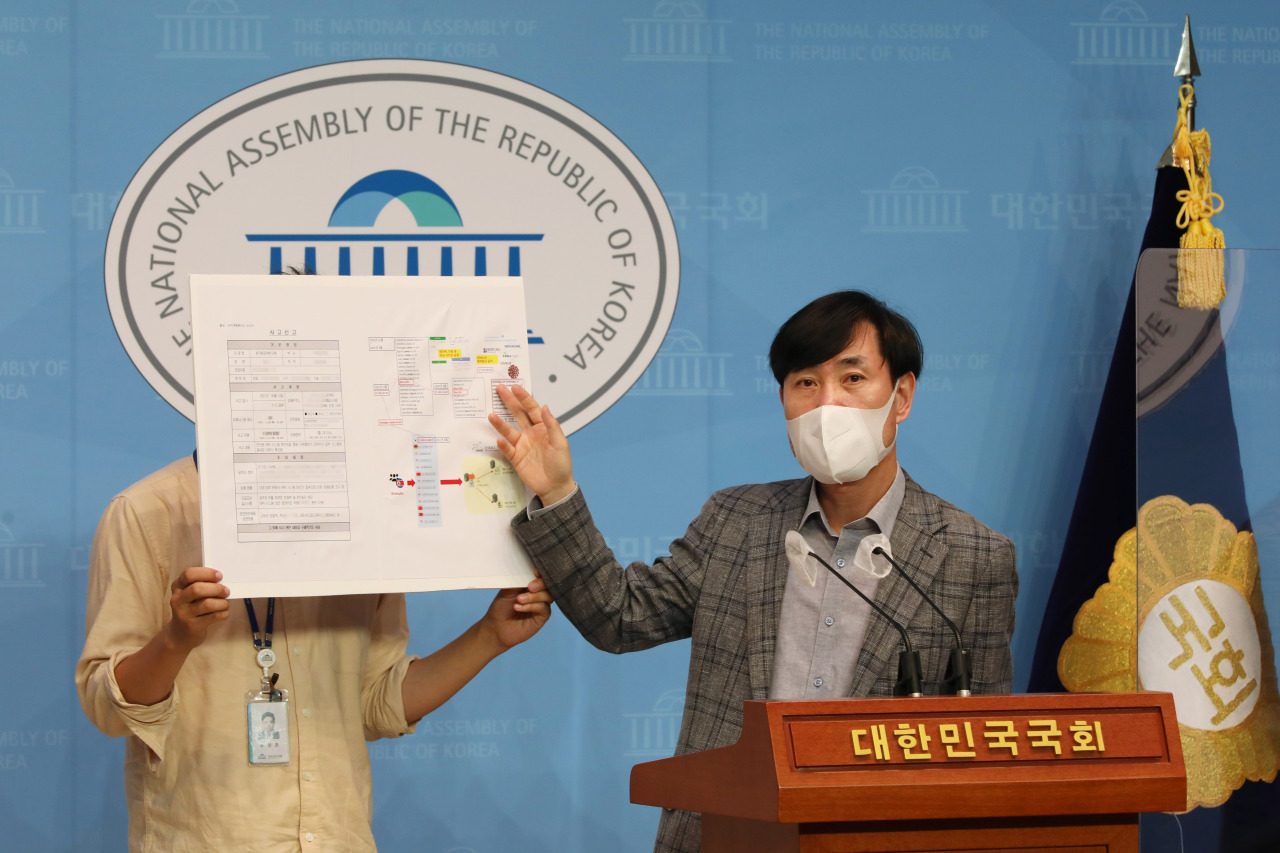
Rep. Ha Tae-keung of the People Power Party, who sits on the parliamentary intelligence committee, held a press conference Friday morning and disclosed information about the alleged cyberattacks on the Korea Atomic Energy Research Institute.
According to the data, 13 unauthorized, external IPs accessed the internal network of KAERI on May 14.
A research group specializing in Pyongyang‘s cyberterrorist activities tracked the IPs and confirmed that some were connected to the server of a hacking unit called “kimsuky” under the North’s Reconnaissance General Bureau, Ha said.
Kimsuky is believed to have led hacking attacks on pharmaceutical companies such as AstraZeneca and Celltrion last year.
The research group also confirmed that some of the IP addresses had previously used the email address of Moon Chung-in, former special advisor to President Moon Jae-in on foreign affairs, which suggests that they are related to the hacking incident of Moon’s email in 2018, Ha said.
“Had the nation’s core technologies on nuclear power been leaked, it could be recorded as a mega security accident comparable to the hacking of the national defense network in 2016,” he said.
Ha also claimed that KAERI tried to cover up the recent hacking attempt by saying there was no such incident when he initially asked them.
“It is impossible to not know that it happened. The government should disclose what happened,” he said.
“Ever since the Moon Jae-in administration took office, the (South Korean) government is trying not to admit hacking (attempts) by North Korea.”
KAERI acknowledged that its internal network has been infiltrated by hackers, but said it was still looking into who was behind the attack, and whether they took certain data.
“We are still investigating which information (the hackers) accessed,” a KAERI official said.
“We tightened network security by setting up firewalls for the external network and updated our internal network.”
By Kim So-hyun (sophie@heraldcorp.com)
Rep. Ha Tae-keung of the People Power Party, who sits on the parliamentary intelligence committee, held a press conference Friday morning and disclosed information about the alleged cyberattacks on the Korea Atomic Energy Research Institute.
According to the data, 13 unauthorized, external IPs accessed the internal network of KAERI on May 14.
A research group specializing in Pyongyang‘s cyberterrorist activities tracked the IPs and confirmed that some were connected to the server of a hacking unit called “kimsuky” under the North’s Reconnaissance General Bureau, Ha said.
Kimsuky is believed to have led hacking attacks on pharmaceutical companies such as AstraZeneca and Celltrion last year.
The research group also confirmed that some of the IP addresses had previously used the email address of Moon Chung-in, former special advisor to President Moon Jae-in on foreign affairs, which suggests that they are related to the hacking incident of Moon’s email in 2018, Ha said.
“Had the nation’s core technologies on nuclear power been leaked, it could be recorded as a mega security accident comparable to the hacking of the national defense network in 2016,” he said.
Ha also claimed that KAERI tried to cover up the recent hacking attempt by saying there was no such incident when he initially asked them.
“It is impossible to not know that it happened. The government should disclose what happened,” he said.
“Ever since the Moon Jae-in administration took office, the (South Korean) government is trying not to admit hacking (attempts) by North Korea.”
KAERI acknowledged that its internal network has been infiltrated by hackers, but said it was still looking into who was behind the attack, and whether they took certain data.
“We are still investigating which information (the hackers) accessed,” a KAERI official said.
“We tightened network security by setting up firewalls for the external network and updated our internal network.”
By Kim So-hyun (sophie@heraldcorp.com)








![[New faces of Assembly] Architect behind ‘audacious initiative’ believes in denuclearized North Korea](http://res.heraldm.com/phpwas/restmb_idxmake.php?idx=644&simg=/content/image/2024/05/01/20240501050627_0.jpg&u=20240502093000)