‘Thought-out policy needed for gray-hat hackers’
Cybersecurity expert says defense policy must incorporate cyberspace
By Korea HeraldPublished : Aug. 3, 2014 - 20:57
This is the fifth installment in a series of articles delving into cybersecurity challenges facing South Korea and the world, and global efforts to tide them over. ― Ed.
In South Korea, one of the world’s most wired nations, there are many cybersavvy youngsters, or “gray-hat hackers,” who flirt with the idea of breaking into computer networks of firms or state entities. Most have no grasp of the illegality of their activities.
These hackers could become cybersecurity specialists, called “white-hat” hackers, or malicious “black-hat” hackers who would pose transnational cybersecurity challenges unless the government addresses them.
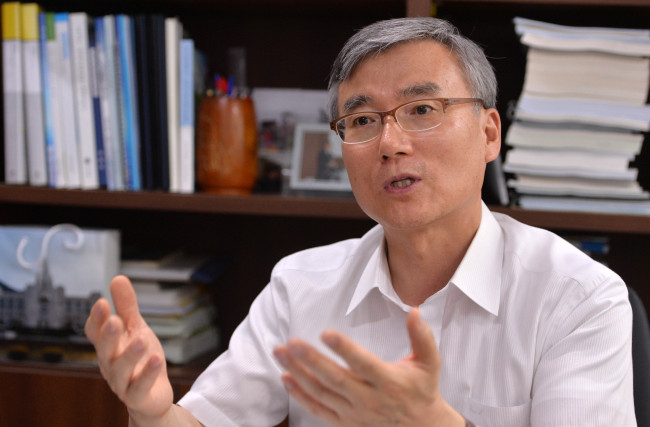
During a recent interview with The Korea Herald, Son Tae-jong, a senior research fellow at the Korea Institute for Defense Analyses, stressed the need for Seoul to craft an effective strategy to help young computer buffs chart positive career paths and contribute to advancing national interests.
“Considering that (gray-hat hackers) are often liberal and defiant, the nation should embrace them with a well-thought-out strategy. Otherwise, they could become cyberterrorists or black-hat hackers who would threaten national security,” said Son.
In South Korea, one of the world’s most wired nations, there are many cybersavvy youngsters, or “gray-hat hackers,” who flirt with the idea of breaking into computer networks of firms or state entities. Most have no grasp of the illegality of their activities.
These hackers could become cybersecurity specialists, called “white-hat” hackers, or malicious “black-hat” hackers who would pose transnational cybersecurity challenges unless the government addresses them.
During a recent interview with The Korea Herald, Son Tae-jong, a senior research fellow at the Korea Institute for Defense Analyses, stressed the need for Seoul to craft an effective strategy to help young computer buffs chart positive career paths and contribute to advancing national interests.
“Considering that (gray-hat hackers) are often liberal and defiant, the nation should embrace them with a well-thought-out strategy. Otherwise, they could become cyberterrorists or black-hat hackers who would threaten national security,” said Son.
Son also underscored the need to promote the positive aspects of the military’s cybersecurity operations as negative views about them have prevailed so far due to the cyberwarfare authorities’ alleged interference in domestic politics.
The following is the interview with Son Tae-jong:
Korea Herald: Korea is one of the world’s most wired nations, yet investment and attention to cybersecurity seem insufficient. What’s your take on this?
Son Tae-jong: With (the media and others) highlighting (political) postings in cyberspace (by the Cyberwarfare Command) during the (2012) presidential election, Koreans, by and large, have come to have negative views about (state involvement in) cybersecurity, although there are many areas in the cyberdomain that deserve closer attention.
Some people even think that the cyberdomain is the exclusive political property of those in power ― the ruling party or other vested interests ― and that they are exploiting the domain to harass the weak, infringe on people’s privacy, steal personal data and so on.
From the standpoint of national interests, there could be times when the state might need to ask for people’s understanding about regulating their activities in cyberspace to some extent. But the overall mood at present makes it hard for the state to promote the positive side of cyberoperations for the benefit of national security. We just got off on the wrong foot and it may take tremendous efforts (to forge positive public views about cybersecurity).
KH: The higher Internet penetration rate a country has, the more vulnerable it seems to be to cyberattacks. Can you comment on South Korea’s vulnerability to cyberattacks?
Son: South Korea has an advanced information technology environment and it has gained international recognition. However, that could make it easy prey for our enemies in cyberspace. In line with its advances in the IT sector, the country should have also paid equal attention to protecting it. But cyberprotection was not high on the priority list. Just like developing states focusing only on national development, (South Korea) has not made sufficient investments in cyberprotection.
Meanwhile, North Korea, despite its poor economic conditions, has focused its national energy on cultivating cyberspecialists and tactics under a strong initiative taken by the coercive socialist regime. As the North concentrates on developing its asymmetric military capabilities such as nuclear weapons and cyberwarfare capabilities, the South faces a growing need to enhance its preparedness against potential cyberattacks.
Should South Korea’s military computer systems come under attack, this could also have a negative impact on its military cooperation with the U.S. and the allies’ joint defense operations. To protect its own information system, the U.S. military could restrict connections between its system and South Korea’s or limit bilateral information exchanges, if the South Korean military’s cybersecurity platform remains vulnerable to attacks.
KH: How do you assess South Korea’s overall cybercapabilities including offensive and defensive skills? What do you think the South should focus more on?
Son: In terms of the timing, I think South Korea was ahead of other nations. The South established its Cyberwarfare Command in 2010, earlier than the U.S. But in terms of the overall cybersecurity capabilities, investments and personnel strengths, there is much room for improvement.
There are many challenges facing South Korea: People have negative views about cyberoperations and some officials still focus mostly on building conventional military power. Also, with the country spending more on public welfare, the government expenditure on defense and cybersecurity tends to dwindle.
Although the Cyberwarfare Command has descended into a sort of political fodder in recent years, it should be regarded as a crucial national strategic asset. In the future, we will see a new form of warfare in which a country can paralyze and distort another country’s decision-making process, damage public sentiment, instill a sense of frustration and defeatism into enemy forces, and eventually win a war without any bloodshed on battlefields. This would be what we call cyberwarfare. South Korea should make more national efforts to build its cybersecurity capabilities in terms of weapons systems, personnel, institutions, military doctrines, training facilities and so on.
KH: Where do you think South Korea’s cybersecurity policy should go? Can you talk about that, particularly with a focus on the legal and institutional aspects?
Son: South Korea needs to designate the cyberdomain as a new military domain (in defense laws) and build well-organized cyber-response systems. I also believe that it is not desirable to use cybercapabilities, which we have built with taxpayers’ money, only during wartime or in the military realm. We need to approach this issue by thinking that the military cybercapabilities should be mustered to support the public and civilian sectors during peacetime as well as in times of crisis.
With regard to legal aspects, the South has well-established laws, rules and guidelines for responses to wartime situations. But these deal mostly with conventional, physical warfare. So it is vital and urgent for the country to incorporate cyberwarfare aspects into those legal frameworks.
The legal systems should be reorganized to allow the military to play an adequate role in conducting cyberoperations during peacetime, times of crisis and wartime. The integrated defense act, for example, deals only with the three traditional domains of land, sea and air. Thus, cyberspace should be integrated in the act and other related laws. There should be a shift in our perceptions of warfare domains, with cyberspace included as another crucial national security realm.
KH: To enhance the overall cybersecurity, cooperation between the state and civilian sectors seems vital. If only the state took the lead in cybersecurity issues, it would not be effective. If the civilian sector took the lead in cybersecurity efforts, it would trigger security issues. What do you think?
Son: There should be legal grounds established so the military can rapidly and effectively respond to cyberattacks based on the expectation that before any conventional warfare, enemy forces might launch large-scale cyberattacks. When establishing legal foundations, there are several issues to be considered: We need to clarify when the military can start leading cyberoperations, and clarify what the military should do during peacetime and wartime.
KH: How do you assess cyberthreats posed by North Korea?
Son: According to a news report last year that cited a U.S. CIA report, the North ranked third in the world in terms of cyberwarfare capabilities. The communist state recognizes cybercapabilities as part of its asymmetric warfare capabilities and is expected to continue to strengthen these capabilities.
South Korea faces difficulties in countering the cybersecurity challenges due to the anonymity of the transnational cyberdomain, and the difficulty of singling out a culprit for cybercrimes. The North’s poor IT environment also makes it difficult for the South to take a retaliatory measure in proportion to the North’s cyberattacks. To add insult to injury, the North could also marshal its cybercapabilities to strengthen its psychological warfare against the South.
KH: Do you think that deterrence in cyberspace is possible? If so, what would be the most effective way to deter cyberaggression?
Son: My personal view is that there have been few ways to successfully deter cyberaggression. All of a sudden, we found that each country was vying to develop cyberwarfare weapons and beef up its offensive capabilities just as major powers competed to develop nuclear arms (during the Cold War). Here we see the intensifying arms race in cyberspace. With current military powers such as the U.S., China and Japan beefing up their cyberwarfare might, the arms race in the cyberdomain has been escalating.
Although deterrence should be achieved through our reliance on international law and diplomacy, or through other peaceful, rational means, major powers appear inclined to pursue deterrence through strength.
Although the U.S. has decreased its defense spending, its spending on cybersecurity has not been reduced. As more nations seem to pursue deterrence through arms races, negative signs have emerged that competition in cyberspace could threaten world peace, just as nuclear weapons did. Again, I want to stress that it is desirable that deterrence should come through international cooperation.
KH: Nurturing white-hat hackers is also very important to strengthen Korea’s cybercapabilities. What do you think?
Son: There are what we call “gray-hat hackers,” who lie between white-hat hackers and black-hat hackers. We should not have teenage gray hackers go through ordinary schooling ― taking school tests such as English tests and the national college entrance exam. We should not let them become simple nine-to-fivers. If we do that, they could end up becoming black-hat hackers whom the nation would have to spend a lot of energy and money to deal with.
We have to come up with ways to lead them to become white-hat hackers and mobilize them to advance corporate or national security interests. Korean gray-hat hackers are well known for their computer skills, with which they have dominated world hacking contests. We should lead them to become our cyberwarriors. As they are liberal and defiant, the nation should embrace them with a thought-out strategy. Otherwise, they could become cyberterrorists or black-hat hackers who would threaten national security.
KH: Any other comments?
Son: What is important is to strengthen cybercooperation with our ally, the U.S., although Seoul, of course, needs to consider its relations with Beijing. Some people say that if we continue collaboration in cyberspace, we will become subordinate to the U.S. in the cyberdomain. But that is the wrong idea.
As South Korea still lacks cyberwarfare capabilities (relative to other world powers), it needs to strengthen cooperation with the U.S. based on their long-running security alliance. The allies need to crank up cooperation in terms of intelligence collection, exchanges of cybertechnologies and establishment of a multilateral cybercooperation mechanism. We can also consider building a multinational cybersecurity system in which the U.S., Japan, Russia, China and Australia participate to jointly respond to and deter North Korean cyberthreats.
Son Tae-jong
● Son has served as a military research fellow at the Korea Institute for Defense Analyses’ Center for Defense Acquisition since 2000. From 2002 to 2007, he led KIDA’s Informatization Policy Research Center.
● With his specialty in informatization, network-centric warfare and cyberwarfare, Son has engaged in a series of KIDA and state research projects including ones on cybersecurity policy planning and defense R&D policies.
● He has coauthored a number of research articles including “Ways to Apply the ‘Systems of Systems Interoperability’ Model to Secure Defense Interoperability” (2011); “The Cybersecurity: Issues and Challenges in the Republic of Korea Ministry of National Defense” (2012); “Network-centric Warfare” (2009); and “A study on the advanced C4ISR systems enabling the NCW in the MND of ROK” (2010).
● He earned a doctorate in computer science from Korea Advanced Institute of Science and Technology in 1999, a master’s degree in computer science from Korea National Defense University in 1988 and a bachelor’s degree in mechanical engineering from Dong-A University in 1987.
By Song Sang-ho (sshluck@heraldcorp.com)
-
Articles by Korea Herald



![[Herald Interview] 'Amid aging population, Korea to invite more young professionals from overseas'](http://res.heraldm.com/phpwas/restmb_idxmake.php?idx=644&simg=/content/image/2024/04/24/20240424050844_0.jpg&u=20240424200058)






![[Hello India] Hyundai Motor vows to boost 'clean mobility' in India](http://res.heraldm.com/phpwas/restmb_idxmake.php?idx=644&simg=/content/image/2024/04/25/20240425050672_0.jpg&u=)





![[Today’s K-pop] NewJeans' single teasers release amid intrigue](http://res.heraldm.com/phpwas/restmb_idxmake.php?idx=642&simg=/content/image/2024/04/26/20240426050575_0.jpg&u=)